Did you forget your Windows user account password? Are you stuck with no access to an administrative account? Do you need to get into your child's (or an employee's) computer for whatever reason? If so, there is an easy way to do it... and all it requires is a Windows Vista/7 DVD, regardless of the actual version of Windows you have installed (an Ubuntu Live CD will also work, but you will need to modify the instructions a bit).
Please keep in mind that unauthorized access to another person's computer is illegal. Be sure to only do this on a computer you own, or on a computer that you have been given authorization to access (such as a client's computer that you are repairing).
Utility Manager and Logon Screensaver
The Windows login screen is quite secure, except for two "glaring" holes: the Utility Manager and the screensaver. The login screensaver, contained in the aptly-named logon.scr file, is the screensaver that is displayed at the login screen after a period of inactivity. The utility manager, contained in the file utilman.exe, is the panel that pops up when you press Win+U or click this button:

Getting a Command Prompt
We need to replace one of these files with a copy of a program that will let us add
or modify user accounts... and what better program to use than cmd.exe,
the Windows command prompt? First we must perform the exploit, and then we must open
the actual command prompt.
- Boot from the Windows Vista or 7 DVD. Note that we will NOT be reinstalling Windows here, and all of your data will be safe.
- (Vista DVD only) Click "Install Now", and go through the installation until you get to the product key screen. Continue without a product key.
- Press Shift+F10. This will open a Windows PE command prompt (Windows PE is a minimalistic version of Windows that is used for the Windows Vista/7 installer, among other things.)
- Type the following commands.
c:
cd \windows\system32
ren utilman.exe utilman.exe.bak
copy cmd.exe utilman.exe
wpeutil reboot - Remove the DVD from your DVD drive and set it aside.
The hacker's command prompt
Once the computer boots up normally, click the aforementioned Utility Manager button (or press Win+U on Windows XP). You should get a command prompt. If you don't, press Alt+Tab, since the login screen is actually a maximized window that can be brought to the front of the Z-order just like any other.
Despite the fact that the command prompt you opened says "Administrator" (well, if you're
on Vista or 7 anyways), it's actually running with SYSTEM privileges (as can be confirmed
by typing whoami into the command prompt and hitting Enter).
NT AUTHORITY\SYSTEM is an account with the highest-possible privileges
on Windows, similar to root on *nix systems.
Gaining Access
From here, there are two paths you can take. You can either create a new user account for accessing the computer's files, or you can reset an existing account's password.
Creating a New Account
Creating a new account is the preferred method to use if you just want access to the
computer. This is done via the NET command. To create a new user account
named "hacker" and assign it administrative privileges, type the following:
net user hacker 12345 /add
net localgroup Administrators hacker /add
Now, click on any existing account and then click "Switch User". If you still don't see "hacker" on the login screen, restart your computer (on Windows XP, you can also press Ctrl+Alt+Del twice to get the classic login prompt and then type the appropriate username and password in). Log in with the password "12345". You can use this account like any other administrative account.
Resetting the Password
If you want to reset the password to an existing account, you can use a similar method. However, please note this important precaution:
WARNING: If you reset a user account's password, the account will PERMANENTLY lose access to encrypted files. Be sure these files are backed up.
To reset your password, you need to first know your internal account name. This name
stays the same regardless of whether you changed your username in Control Panel.
To see a list of names, type net user.
Now, all it takes is one command. net user username 12345, where "username"
is the internal account name and "12345" is the password you want. You should be able
to log in right away without rebooting.
Preventing Attack
You're probably thinking "oh great, now anyone can access all of my personal files!" Not so fast. Windows contains several safeguards to prevent this.
Encrypting Files (Some Editions Only)
Did you read the red warning box above? When a password is reset, the account loses access to any encrypted files and folders. Thus, if you have any private data that you would rather lose than letting it get into the wrong hands, this option is for you. You can apply the "Encrypt" attribute to any file or folder; this allows you to access it normally, but prevents any other account from accessing it.
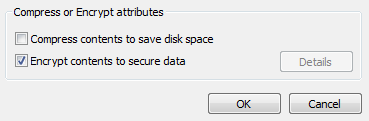
There are two things to note here. One, this option is only available in some editions of Windows (Windows XP Professional, Media Center Edition, Tablet PC Edition; Windows Vista Business, Enterprise, Ultimate; Windows 7 Professional, Enterprise, Ultimate; all server variants of Windows). Two, you can (and most definitely should!) back up your EFS encryption certificate and key using certmgr.msc, so that you will be able to access your files somehow.
Full Disk Encryption
Another alternative is to use full-disk encryption such as BitLocker (available in Enterprise and Ultimate editions of Windows Vista and Windows 7, as well as Windows Server 2008). If the hard drive is protected by full-disk encryption, nobody will be able to access any of the files in your system32 folder, and thus it will be impossible to replace utilman.exe.
Finishing Up
It is crucial that you restore the proper utilman.exe file, or anyone will be able to easily create new user accounts at the login screen. Also, if you created new user accounts, it may be desirable to remove them.
Removing User Accounts
Log out of your "hacker" account, if you created it using the steps above. Open the
command prompt again, and type net user hacker /delete.
But that's not all. There is still a user account folder in C:\Users (Windows
Vista/7) or C:\Documents and Settings. We need to remove it, and make sure
that it's the right one. Type the following into Command Prompt:
cd \users (or cd "\documents and settings" on XP)
dir
Find the name "hacker" in the list. If you see several names beginning with "hacker", such as "hacker.001", "hacker.002", etc., do not touch them and skip this step, since you may end up deleting someone else's account. Otherwise, type:
del hacker
rmdir hacker
IMPORTANT: Restore utilman.exe
Insert your Windows Vista/7 DVD and follow the steps above for getting a Windows PE command prompt. This time, type the following commands to restore the backup of utilman.exe.
c:
cd \windows\system32
del utilman.exe
ren utilman.exe.bak utilman.exe
wpeutil reboot
And you're done.
![[XML]](/images/xml.png)
Comments (4)
Then tried Youtube and advanced search to filter out old videos... this method worked for me perfectly:
http://www.youtube.com/watch?v=6fe5cTyZ_ms
Hope this helps!
I can't change directories to system32 using cd \windows\system32. Do you have suggestions?
Leave a comment